Claude Code Flaw - RCE Vulnerability
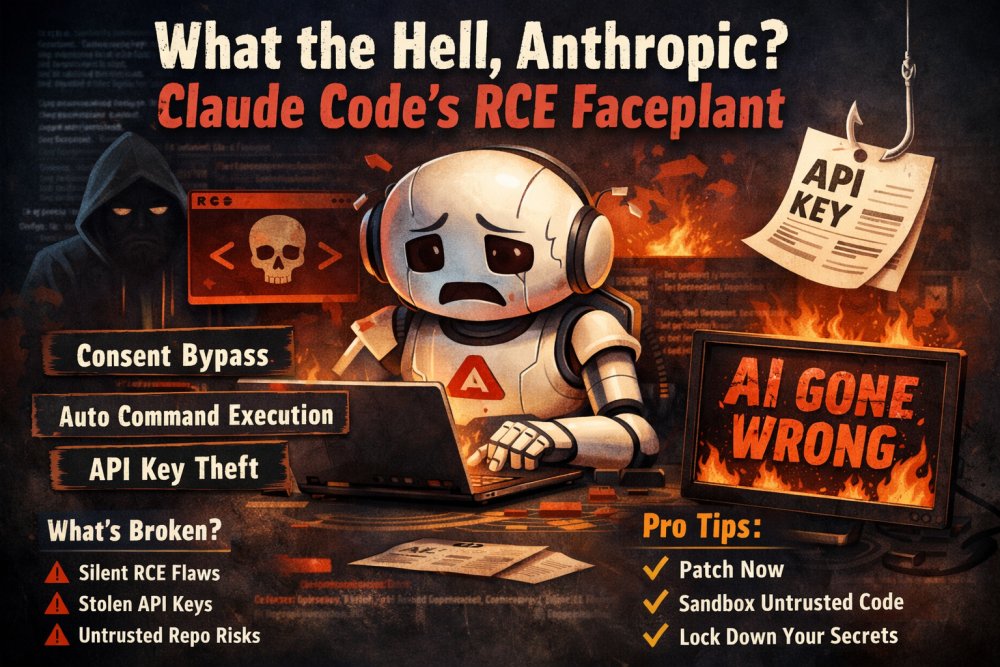
Anthropic shipped a shiny “developer assistant” called Claude Code, and for a brief, glorious moment it apparently believed the best way to help developers was by letting attackers run commands on their machines. Researchers reported multiple flaws that enabled remote code execution (RCE) and even API key exfiltration from seemingly routine workflows like opening a repository.
The short version
If you used Claude Code on an untrusted project, it could be convinced to execute arbitrary shell commands and leak secrets. Not because you clicked “yes, please ruin my day,” but because the trust boundaries were… aspirational.
So what broke?
The report describes multiple issues, but they rhyme with a common theme: Claude Code treated project-controlled configuration and hooks like friendly suggestions instead of hostile input.
1) Consent bypass that leads to RCE
One flaw allowed command execution without the user meaningfully consenting. In other words, a repo could smuggle in behavior that results in running attacker-controlled commands. If your threat model includes “opening code from the internet,” this is not a fun surprise.
2) Shell command execution triggered by a repo
Another issue boiled down to this: open or initialize a project, and malicious repo contents could cause commands to run automatically. That’s the classic supply chain nightmare, now with the added comedy of an AI tool acting as the execution engine.
3) API key exfiltration before the trust prompt
The crown jewel: a scenario where Claude Code could be coaxed into making API requests to an attacker-controlled endpoint before the user sees (or approves) the trust prompt. Translation: your Anthropic API key can be walking out the door while you’re still reading the dialog box.
Why this is extra bad
Developer tools sit in a privileged place. They see your filesystem. They see your tokens. They run on machines that have access to production credentials because humans are messy and time is short. When you bolt “agentic” behavior on top of that, you’re basically building a very polite automation layer that can also become a very efficient attacker assistant if you get the boundaries wrong.
The painful part is that none of this is exotic. We already know how this movie ends: untrusted inputs, implicit execution, credentials in environment variables, and a tool that assumes the project is “probably fine.” The only thing new here is that the tool’s marketing says “AI” and the feature list says “productivity,” while the bug class says “please stop cloning random repos.”
Did Anthropic fix it?
The issues were reported and patches were shipped. Good. That’s the expected outcome, not a bonus feature. The bigger lesson is what it took to get here: a developer-focused tool that executes commands needs paranoid defaults, strict prompting discipline, and airtight sequencing for trust gates. If secrets can be sent before trust is established, then the trust prompt is theater.
What you should do (yes, you)
- Update Claude Code immediately if you use it.
- Treat repos as hostile until proven otherwise, especially when tools auto-run “helpful” hooks.
- Keep API keys scoped and rotated, and avoid long-lived tokens sitting in easy-to-exfiltrate places.
- Run risky tooling in a sandbox or separate environment when evaluating untrusted code.
Final verdict
Claude Code is a neat idea wrapped around a very old security lesson: execution is a privilege, not a convenience. If your AI assistant can run commands, it must also be extremely good at not running commands. Anthropic learned this the hard way, and developers got an unwanted reminder that “agentic” without “guardrails” is just a fancy word for “attack surface.”
Source: The Hacker News article on Claude Code flaws allowing remote code execution and API key exfiltration.